Dark Net Army and Online Network Strategies
The Dark Net Army represents a complex and evolving phenomenon within the realm of cyber activities, characterized by coordinated groups operating in hidden online spaces. These entities often leverage encrypted communication channels and anonymity tools to execute various objectives, ranging from cybercrime to information warfare. Understanding their operational methods provides valuable insights into broader online network strategies employed across different digital environments.
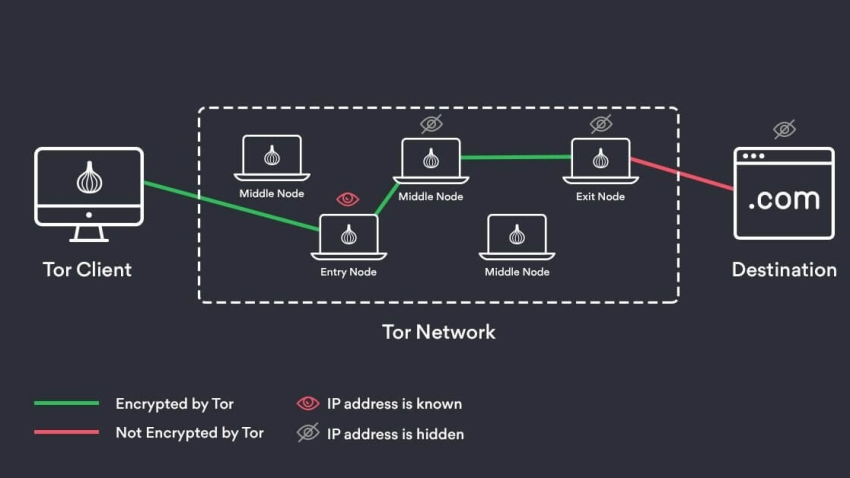
At the core of Dark Net Army operations lies the use of decentralized networks that obscure user identities and locations. This approach enhances security for participants while complicating efforts by law enforcement to track or dismantle such groups. The adoption of technologies like Tor (The Onion Router) enables access to dark web marketplaces, forums, and communication platforms where members exchange resources, share intelligence, or recruit new participants. In this context, operational secrecy is paramount; encryption protocols protect messages from interception and ensure that sensitive data remains confidential.
Online network strategies utilized by these actors emphasize resilience and adaptability. Rather than relying on centralized command structures vulnerable to disruption, they often implement distributed models that allow individual cells or nodes to operate autonomously yet remain interconnected through secure channels. This structure mitigates risks associated with infiltration or shutdowns while facilitating rapid response capabilities when facing external threats or opportunities.
Information dissemination plays a crucial role in maintaining influence within target communities or adversaries. Propaganda campaigns may be conducted subtly through social media manipulation or direct engagement on niche forums accessible via both surface web and dark net layers. Such tactics aim not only at recruiting sympathizers but also at sowing discord among opponents by spreading disinformation or exploiting existing societal fractures.
Financial transactions supporting these operations frequently utilize cryptocurrencies due to their pseudonymous nature and ease of cross-border transfers without traditional banking oversight. This financial strategy aligns with broader trends in illicit online economies where anonymity is essential for concealing funding sources and expenditure patterns.
Countermeasures against Dark Net darknet army activities involve a combination of technological innovation, policy development, and international cooperation. Cybersecurity professionals employ advanced analytics to detect anomalies indicative of coordinated attacks or illicit exchanges within encrypted networks. Meanwhile, governments work toward harmonizing legal frameworks that address jurisdictional challenges inherent in cyberspace governance.
In summary, the Dark Net Army exemplifies sophisticated use of clandestine online infrastructures combined with strategic networking principles designed for persistence under scrutiny. Their methodologies highlight significant challenges faced by defenders seeking to preserve digital security without compromising privacy rights fundamental to open societies. Continued research into these dynamics fosters improved understanding necessary for developing effective counterstrategies tailored to an increasingly interconnected world landscape marked by both opportunity and risk in cyberspace domains.
